SOC Analysts work to ensure cybersecurity for large organizations and firms. They analyze security measures and implement cybersecurity strategies to protect data from hackers and malicious attacks. Let’s take a closer look at what they do.
What is SOC and what’s the role of SOC analysts?
An emerging phrase in the cybersecurity world currently is ‘SOC Analyst’. Being a relatively new but growing role, many are not sure what a SOC analyst does, or what ‘SOC’ even stands for.
A Security Operations Center (SOC) is a 24-hour control center in charge of security and threat analysis for an organization. It is essentially a structure in place for large firms and organizations looking to strictly protect their cyber assets.
Within these centers, security experts always have the situation in view so that threats and incidents can be identified quickly and reacted to appropriately.
Individual IT security tools such as firewalls, malicious code scanners or intrusion detection systems are no longer sufficient to guarantee comprehensive protection. This has created an upswing in investments towards personalized integrated measures such as SOCs.
A SOC is also operated “as a service”, whereby different names are used: Cyber Defense Center, Security Center, Cyber Defense Center, LKRZV and other names.
Hire an SOC analyst for your project » Find SOA analysts now 🔍
What are the responsibilities of a SOC Analyst
A Security Operation Center Analyst is essentially responsible for all activities that occur within the SOC. Analysts in Security Operations work with security engineers and SOC managers to provide situational awareness via detection, containment, and remediation of IT threats.
With the increase in cyber threats and malicious data hacks, businesses are becoming more and more vulnerable to threats. This has significantly increased the importance of a SOC Analyst. For those in cybersecurity, it can be a dynamic and lucrative role.
SOC Analysts collaborate with other team members to detect and respond to information security incidents, develop, maintain, and follow procedures for security event alerting, and participate in security investigations.
Furthermore, SOC Analysts analyze and respond to undisclosed hardware and software vulnerabilities. They also investigate, document, and report on security issues and emerging trends. In essence, they act as ‘security advisors’ for an organization.
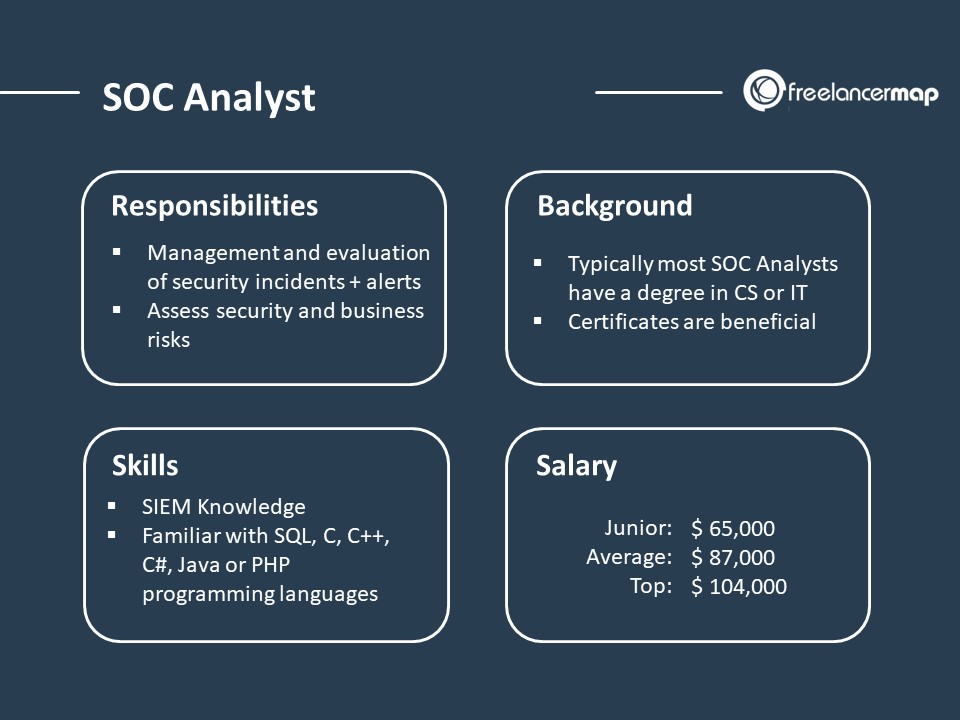
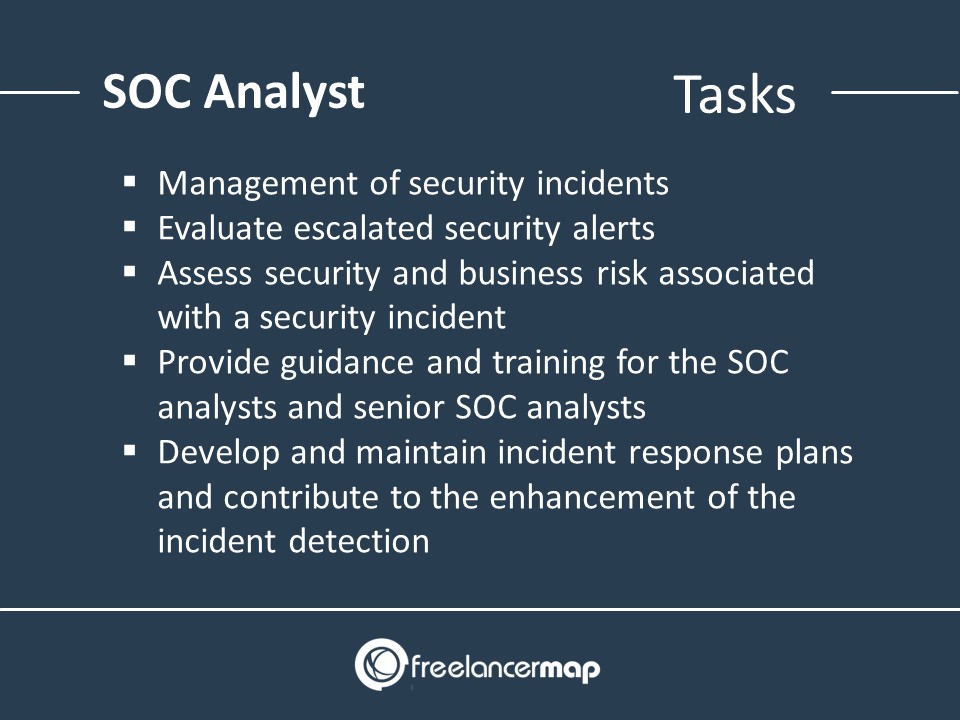
Critical responsibilities of a SOC Analyst include:
- Management of security incidents during all stages of the incident management process including an in-depth analysis
- Evaluate escalated security alerts from senior SOC analysts
- Assess security and business risk associated with a security
incident and coordinate containment, eradication, recovery,
investigation and response measures - Assure an appropriate tracking, documentation, closure and post-incident reporting and review of incidents
- Provide guidance and training for the SOC analysts and senior SOC analysts
- Develop and maintain incident response plans and contribute to the enhancement of the incident detection
SOC Analyst Skills

Technological advances have become increasingly profound in the past few years. As such anyone working cybersecurity needs to stay up to date with emerging technologies. Automation in cybersecurity will eventually make tasks involving the analysis of raw data superfluous. At the same time, however, new professional fields will open up that require special expertise.
Over the next five years, the ability of cybersecurity experts to understand and critically question machine learning parameters and processes will become increasingly important. To be able to train and improve machine learning algorithms, extensive special knowledge is required.
Because risks need to be seen in a larger, more rapidly changing
context, SOC Analysts need to use priority logic tools for much larger
data sets. They also need to have extensive data science knowledge to
make the right decisions and to develop a solid prevention strategy against attacks.
Required skills for a SOC Analyst:
- Knowledge of Security Information and Event Management (SIEM)
- Familiar with SQL, C, C++, C#, Java or PHP programming languages
- TCP/IP, computer networking, routing, and switching
- IDS/IPS, penetration and vulnerability testing
- Firewall and intrusion detection/prevention protocols
- Windows, UNIX and Linux operating systems
- Network protocols and packet analysis tools
- Anti-virus and anti-malware
SOC Analyst Background and Education
The work experience and degree requirements to be a SOC Analyst will vary from organization to organization, but in general, most companies require a Bachelor’s degree in Computer Science or a related field as well as 1-3 years of work experience.
Desired certifications can include:
- Security+ (beginner)
- CEH (intermediate)
- CASP (intermediate)
- GIAC (intermediate)
- CISSP (advanced)
How much does a SOC Analyst make?
Salaries for SOC Analysts depends on the work skills and experience you have. In general, however, the salary of a Junior SOC Analyst is about $65,000 per year. With a few years of experience and increased skills, analysts can hope to earn about $87,000 on average. A Senior SOC Analyst has the potential to earn up to $104,000.
Salaries of SOC Analysts:
| Junior | $65,000 |
| Average | $87,000 |
| Senior | $104,000 |
How much do Freelance SOC Analysts charge?
SOC analysts on freelancermap charge on average:
Rates in this field range between $33 and $106/hour for most freelancers.
The daily rate for SOC analysts (8 working hours) would be around:
Other interesting profiles
- What Does A Big Data Specialist Do?
- What Does A Cryptographer Do?
- What Does An Ethical Hacker Do?
- What does an HRIS Analyst do?
- What Does A Computational Linguist Do?
» More job profiles in Data Science & Analysis
Looking to hire a skilled freelancer? Create your account in just 2 minutes and start connecting with top talent worldwide!
Sign up for free